Link roundup for 2019-09-08
Welcome to this week's roundup. From now on I'll be including an estimated read time for each link, so you have a general idea of what to expect.
You will start seeing the term Rabbit Hole, or RH for short, to indicate those links that can lead to hours and hours of new and interesting discoveries.
More on the iOS implant
In A message about iOS security (2 min, via), Apple responds to the terrifying implant that was reported last week.
First, the sophisticated attack was narrowly focused, not a broad-based exploit of iPhones "en masse" as described. The attack affected fewer than a dozen websites that focus on content related to the Uighur community.
[...]
Google's post, issued six months after iOS patches were released [...] We fixed the vulnerabilities in question in February — working extremely quickly to resolve the issue just 10 days after we learned about it
A bit of damage control and down-toning Google's report, however, I still stand by my take on it.
Apple Music official web app
Apple Music launches on the web (via)
Finally.
Apple is serious about competing with Spotify, which is good. However, I couldn't make it work on Linux (Chrome and Firefox). Let's see if they support these configurations soon.
Librem 5 phone shipping
Librem 5 Shipping Announcement (1 min, via)
The Librem 5 is here. I'm very curious as to how the phone is going to turn out and surely will have an eye opened for the first reviews.
Google keeps selling their user data
Brave uncovers Google's GDPR workaround (10 min, via)
Google claims to prevent the many companies that use its real-time bidding ad (RTB) system, who receive
sensitive data about website visitors, from combining their profiles about those visitors. It also announced that it had stopped sharing pseudonymous identifiers that could help these companies more easily identify an individual, apparently in response to the advent of the GDPR.But in fact, Brave's new evidence reveals that Google allowed not only one additional party, but many, to match with Google identifiers. The evidence further reveals that Google allowed multiple parties to match their identifiers for the data subject with each other.
Don't use Google.
How does BitTorrent work?
How Does BitTorrent Work? a Plain English Guide (15 min) is a long and comprehensive explanation of the BitTorrent protocol, written in a language that most engineers will understand. There are many emojis and beautiful illustrations, but this is definitely not something you can send your mom.
How Netflix uses Python
Python at Netflix (5 min, via) details a series of Python tools and how they are used at Netflix.
Some may be interesting for you, some may be not. Skim the text and focus on whatever catches your eye!
How Tetris decides which piece comes next
The history of Tetris randomizers (1 min, via) is a short and interesting read on how Tetris chooses the next piece, with pros and cons of each approach which affect released games, like the NES version.
If you want to enter the Tetris Nirvana, check out Tetris.wiki (RH, via)
A historical tour of software and websites
The Version Museum (RH) "showcases the visual history of popular websites, operating systems, applications, and games that have shaped our lives."
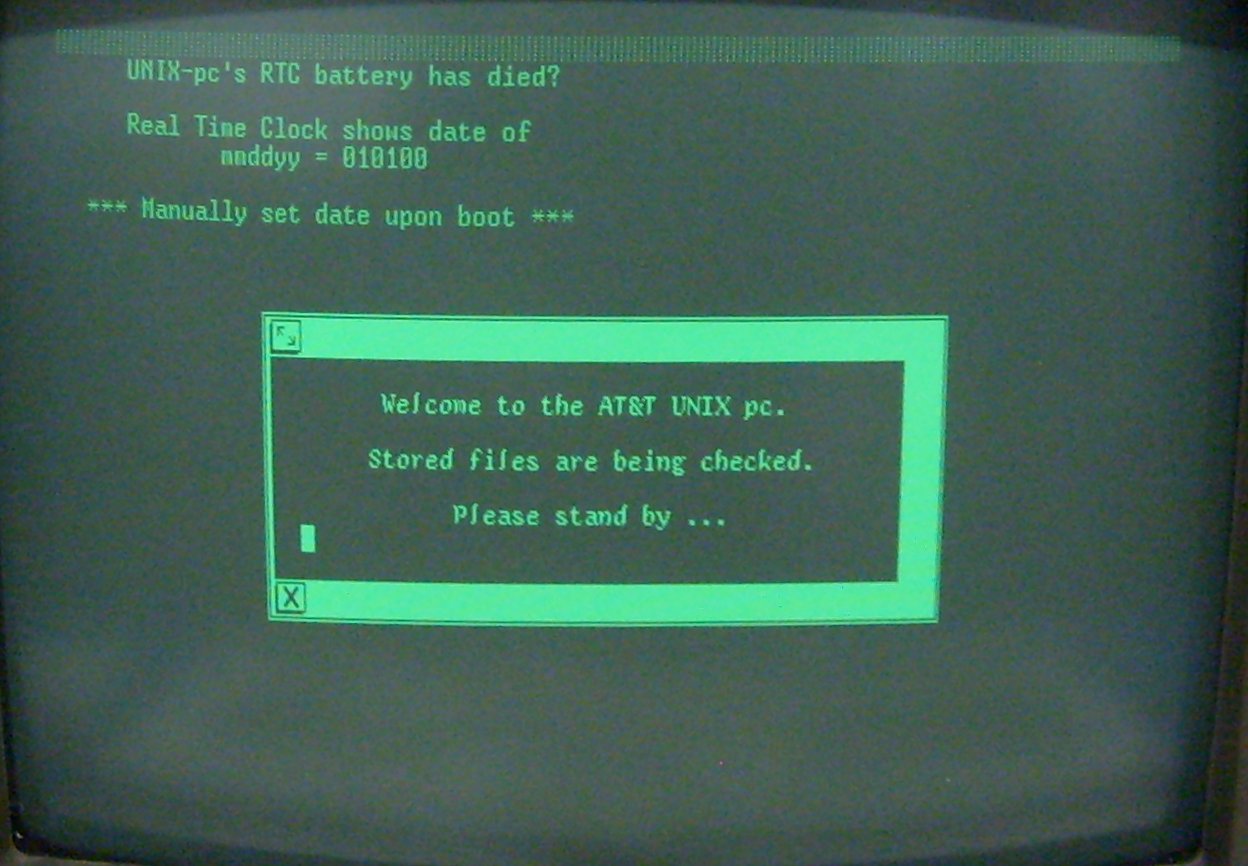
If you like this website, you can't miss the GUIdebook Gallery and the GUI Gallery, both of them are excellent, and especially the latter contains literal screen shots of very old, obscure systems.
More on deepfakes
The Verge reports that Another convincing deepfake app goes viral prompting immediate privacy backlash (1 min), and TheNextWeb informs that Fraudsters deepfake CEO’s voice to trick manager into transferring $243,000 (1 min)
We all knew this day would arrive, and now it's here—it's been here for a couple years now, really.

In the 90s, Photoshop became a verb that stands for changing a picture in such a way that the end result is fake but believable. Technology now allows us to do the same with video and audio.
This is a very interesting social challenge. Not being able to trust any picture/video/audio will for sure change concepts like proof and deniability which are core for law and society.
Cool CSV utils for the command line
eBay has a Github repo (1 min read, more to try the code, via) with sort of a "framework" to handle csv/tsv files from the command line.
User JimmyRuska also contributed with more tools and other users have linked to their favorite scripts in the comments. I highly recommend you check out the discussion if you work with csv files regularly. Being able to transform data quickly on the terminal is a true superpower.
Of course, you can convert any csv file into a SQL database using sqlite's .mode csv, which
I recommend even more for huge datasets that don't fit in memory.
Read time: 1 minute to check it out, more if you actually run the code
Learning how to read
User vilvadot asks HN how do others read a book (5 min to RH)
The answers are very interesting, and user guidoism recommends How to Read a Book: The Classic Guide to Intelligent Reading (Wikipedia link), and user Scarbutt links to a University of Michigan's 11-page document How to Read a Book, v5.0
Check it out if you want to improve your reading techniques
Tags: roundup