Link roundup for 2019-09-15
Twitter CEO gets his Twitter account hacked
Hackers Hit Twitter C.E.O. Jack Dorsey in a 'SIM Swap.' You're at Risk, Too. (5 min, via)
Here's how it works:
Sometimes hackers get phone numbers by calling a customer help line for a phone carrier and pretending to be the intended victim. In other recent incidents, hacking crews have paid off phone company employees to do the switches for them, often for as little as $100 for each phone number.
Once the hackers have control of the phone number, they ask companies like Twitter and Google to send a temporary login code, via text message, to the victim’s phone. Most major online services are willing to send those messages to help users who have lost their passwords.
But the temporary code is sent to the hackers.
2FA over SMS is not the best, but not the worst. The problem is that Twitter's implementation was bad, as it allowed you to reset anybody's password with —this is key— only their phone number.
HN user zaroth explains it well:
Twitter uses SMS as a single factor, because you can reset the password with only access to the text message. If Twitter was using SMS only as a 2nd factor, this attack would not have worked without also knowing Jack’s password or having access to his email. Twitter’s password reset function could require an SMS code and then send a password reset email to complete the process.
While user fulafel summarizes it in a tweet-like sentence:
It's really ½FA, worse than 1FA authentication because it's sufficient to clear any 1 of the 2 factors.
Favorite old books?
Ask HN: What are your favorite books or essays written at least 100 years ago? (10 min - RH) user marceee0901 asks an interesting question, and the replies are very interesting, too.
Some non-tech books surface to the top, like:
- The Count of Monte Cristo
- Meditations
- The Prince
- Anna Karenina
And user cbailes suggests a site I wasn't aware of: The Hacker Classics, a list of HN links with a date on the title, e.g. (1928), sorted by this date.
Facebook fighting deepfakes
In Creating a data set and a challenge for deepfakes (2 min, via), Facebook announces that they are committing $10M to create a dataset of True Positive deepfakes so researchers can develop tools to detect them.
Thanks, Facebook.
Firefox sending DNS queries to Cloudflare
What's next in making Encrypted DNS-over-HTTPS the Default (2 min, via) Mozilla explains why they will send all your DNS queries to Cloudflare.
I do not like this on the slightest bit. The current DNS system is good as it is now; you can choose to trust
your ISP, typically the default choice, or use a third party system like Google's 8.8.8.8
However, the browser should definitely NOT run their own DNS subsystem and bypass the OS or network default.
Neither should us collectively, as a matter of principle, give too much power over the internet infrastructure to a single company. We already made this mistake with Google (search and mail) and Facebook (personal data) and, well, I rest my case.
And, though not related to my point, let's not forget that Cloudflare apocalyptically screwed up in 2017 by unknowingly leaking HTTPS traffic in plain text
Overall, a bad idea, Mozilla, and you should step back on this.
The Senior Engineer's Checklist
A Senior Engineer's CheckList (5 min, via) is a good compilation of both technical and human tasks that a senior engineer should be aware of.
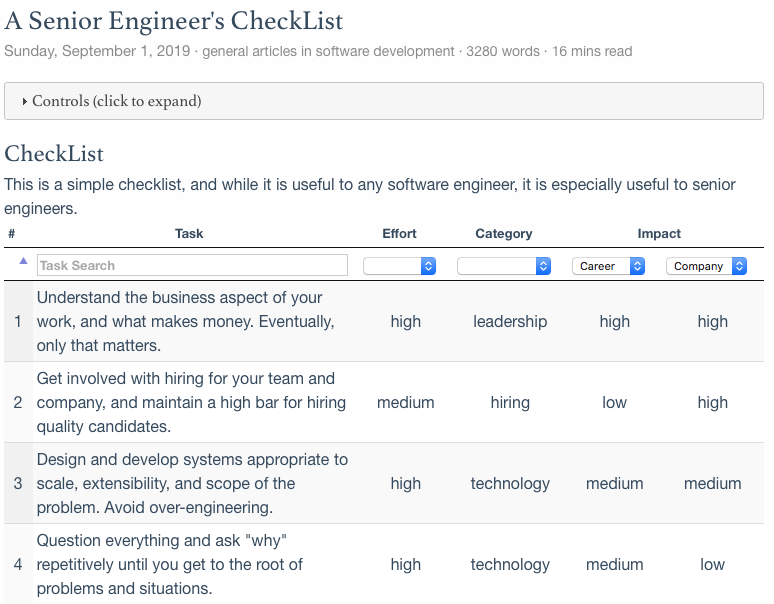
Really good read, check the author's comments at the via link.
Sunsetting Python 2
Sunsetting Python 2 (2 min) explains why Python 2 needs to die. And it does so in an excellent and thoughtful way, providing real answers to real questions that Python 2 users may have, both experts and novices.
I especially like the last two FAQ points:
I didn't hear anything about this till just now. Where did you announce it?
and
How can I make sure announcements like this don't surprise me again?
Finally, I found it brilliant how they emphasize that this decision will benefit the whole community by optimizing volunteers' time. The word volunteer appears all over the FAQ, which I think is a great way to avoid pointless discussions: volunteers don't owe you anything, please use Python 3 now.
A civ1 clone in Excel
I'm creating a Civ1 clone - in Excel (RH, via)
Super impressive and really cool!
A full featured toy OS that runs Doom
Soso, a simple unix-like operating system (1 min, via) is a nice toy OS with a lot of features:
Soso is a 32-bit x86 operating system and its features are
- Multitasking with processes and threads
- Memory Paging with 4MB pages
- Kernelspace (runs in ring0) and userspace (runs in ring3) are separated
- Virtual File System
- FAT32 filesystem using FatFs
- System calls
- Libc (Newlib is ported with only basic calls like open, read,..)
- Userspace programs as ELF files
- mmap support
- Framebuffer graphics (userspace can access with mmap)
- Shared memory
Soso has Libc, so existing applications depending only on a small part of Libc can easly be ported to Soso. I have managed to build and run Lua and Doom on Soso!
You can download an ISO and run it with qemu, go ahead and try it!
Tags: roundup