Links for 2019-10-13
No common topic this week. Enjoy the links!
New Linux laptops with open source firmware 🔗
System76 Will Begin Shipping 2 Linux Laptops With Coreboot-Based Open Source Firmware (2 min, via)
My endgame is to retire early and create an ecosystem of free hardware + software for a laptop, phone and could environment, like iCloud but totally self-hosted.
Meanwhile, we have to be satisfied with small advances like these laptops running Coreboot.
Kudos to System76, and let's hope the market moves towards this goal.
New graphical toy OS 🔗
SerenityOS: From zero to HTML in a year (2 min), is a visual tour through the development of SerenityOS, a toy OS with graphical capabilities, now able of rendering a webpage using its own web browser.
As a fan of toy OSs, this is awesome.
Ken Thompson's password 🔗
Ken Thompson's Unix password (2 min, via) explains how Nigel Williams hacked Ken Thompson's extremely secure Unix password and it turns out to be a chess move!
From: Nigel Williams Subject: Re: [TUHS] Recovered /etc/passwd files
ken is done:
ZghOT0eRm4U9s:p/q2-q4!
took 4+ days on an AMD Radeon Vega64 running hashcat at about 930MH/s during that time (those familiar know the hash-rate fluctuates and slows down towards the end).
D-Link routers will remain vulnerable 🔗
D-Link Home Routers Open to Remote Takeover Will Remain Unpatched (1 min, via)
I am just going to quote HN user jjguy:
This is the new normal, folks. Consumer technology is manufactured for six to twelve months, but live in our homes for three to five years. Today's manufacturers cannot afford to update software for hardware devices they have already moved on from. Changing that requires a significant upheaval in their business models.
This applies to every "connected device:" printers, cell phones, home routers, refrigerators, thermostats -- you name it.
Your router is your gateway to the Internet. Any flaws on its software will open your home computers and phones to remote attackers.
There is little we can do, except starting to treat our routers like any other computer: make sure it's updated regularly, and when it does not get any security updates anymore, replace it with a newer model.
Twitter misusing 2FA phone numbers 🔗
Twitter admits it used two-factor phone numbers and emails for serving targeted ads (1 min, via)
Only one month ago, Twitter's CEO Jack's account was hacked exploiting his 2FA phone number via "SIM swap" attack.
Now we discover that, like Facebook did, Twitter also used the phone you provided for 2FA to target you with ads.
Shame on Twitter, this is an absolutely shitty practice which will backfire by letting users associate 2FA with a bad thing.
As HN user danShumway explains:
Virtually the entire security industry agrees that using phone numbers for account security is an antipattern because of sim-jacking, and yet swaths of the biggest tech companies in the industry do it anyway.
[...]
In theory, a 2FA over SMS is better than nothing. In practice, it trains customers to be insecure and should be avoided. It trains customers to think that identity verification over text is OK. In practice, you can't trust companies not to use it for advertising, or to start using it as identity verification in the future. In practice, there are very, very few legitimate reasons why a company should ever need my phone number, and pretty much none of them have anything to do with security. 99% of your users should be using a 2FA app instead of a phone number.
Remote exploit on the wild for Android phones 🔗
New 0-Day Flaw Affecting Most Android Phones Being Exploited in the Wild (2 min)
The zero-day is a use-after-free vulnerability in the Android kernel's binder driver that can allow a local privileged attacker or an app to escalate their privileges to gain root access to a vulnerable device and potentially take full remote control of the device.
According to the researcher, since the issue is "accessible from inside the Chrome sandbox," the Android kernel zero-day vulnerability can also be exploited remotely by combining it with a separate Chrome rendering flaw.
Therefore, most Android devices manufactured and sold by a majority of vendors with the unpatched kernel are still vulnerable to this vulnerability even after having the latest Android updates
- Pixel 1
- Pixel 1 XL
- Pixel 2
- Pixel 2 XL
- Huawei P20
- Xiaomi Redmi 5A
- Xiaomi Redmi Note 5
- Xiaomi A1
- Oppo A3
- Moto Z3
- Oreo LG phones
- Samsung S7
- Samsung S8
- Samsung S9
To be noted, Pixel 3, 3 XL, and 3a devices running the latest Android kernels are not vulnerable to the issue.
This is really, really bad. Update as soon as the patches are released, and don't browse untrusted websites meanwhile.
Dockerizing ancient OSs 🔗
Resurrecting Ancient Operating Systems on Debian, Raspberry Pi, and Docker (1 min, via) is a quick note where the author explains how he has dockerized ancient OSs repo to replicate these old environments and play with them in the modern era.
I like this idea a lot and, actually, I have my own folder of virtualised systems with which I play from time to time. I have a perfect replica of my old computers (a DOS + Win31, a Win98 and a WinXP) and run them regularly to feel that good nostalgia.
Your crappy app wastes my brain glucose 🔗
Your app makes me fat (2013, 5 min, via)
This is an extremely interesting article on popular psychology and how willpower is a finite resource which gets depleted.
Willpower and cognitive processing draw from the same pool of resources.
Spend hours at work on a tricky design problem? You're more likely to stop at Burger King on the drive home. Hold back from saying what you really think during one of those long-ass, painful meetings? You'll struggle with the code you write later that day.
Since both willpower/self-control and cognitive tasks drain the same tank, deplete it over here, pay the price over there. One pool. One pool of scarce, precious, easily-depleted resources. If you spend the day exercising self-control (angry customers, clueless co-workers), by the time you get home your cog resource tank is flashing E.
Remember these conclusions: since I read about that link between glucose depletion in the brain and willpower I have been much more aware of my cravings and how to avoid succumbing to them.
The rise of Matebooks 🔗
Void Linux (musl) on the Huawei Matebook X Pro (5 min) is a good review of the Matebook, with some bonus opinions on Void Linux.
I've mentioned many times that I'm unhappy with the current state of Apple hardware, and I have been looking for alternatives.
Old Lenovos are cheap, newer Lenovos are pretty good, and it's nice to know that there's a high quality, affordable laptop in between them.
Remembering the BBSs 🔗
BBSes: Partying Online Like It's 1989 (10 min, via)
The BBS era is one I barely missed, as my early Internet experiences happened around 1996 via IRC, mail and the early web. The article reminisces of this primeval and very popular form of communication that catered to many niches.
On a side note, I just discovered Paleotronic, and it's a great source of retro nostalgia. The topics are interesting, the text is accessible, and it's full of pictures from old magazines. You will probably see it linked a lot here!
A cynical take on HN 🔗
webshit weekly is a weekly commentary on the top HN links.
I really like the author's cynical take, his sense of humor, and the way he interprets comments on the funniest and worst possible way.
You will find gems like:
(Apple Hides Taiwan Flag in Hong Kong)
Whether an old person falls over or a young person stands up, Apple will call the cops.
(Google Cloud is down)
Nobody considers the obvious root cause: Google, being unable to embed ads into TCP packets, has discontinued the product.
(Comparing the Same Project in Rust, Haskell, C++, Python, Scala and OCaml)
Some children play programming language pokemon.
(Facebook reveals its cryptocurrency Libra)
Facebook, unsatisfied with being an unregulated newspaper, post office, and telephone service, decides the only way to recover from years of user-abuse scandals is to become an unregulated bank.
Privacy under attack by US, UK, AU govts 🔗
The Open Letter from the Governments of US, UK, and Australia to Facebook is An All-Out Attack on Encryption (1 min, via)
The EFF explains:
Top law enforcement officials in the United States, United Kingdom, and Australia told Facebook today that they want backdoor access to all encrypted messages sent on all its platforms. In an open letter, these governments called on Mark Zuckerberg to stop Facebook's plan to introduce end-to-end encryption on all of the company's messaging products and instead promise that it will "enable law enforcement to obtain lawful access to content in a readable and usable format."
I don't have much more to add other than linking to my 2015 text on "Think of the terrorists" is the new "Think of the children"
Followup
More problems with Catalina 🔗
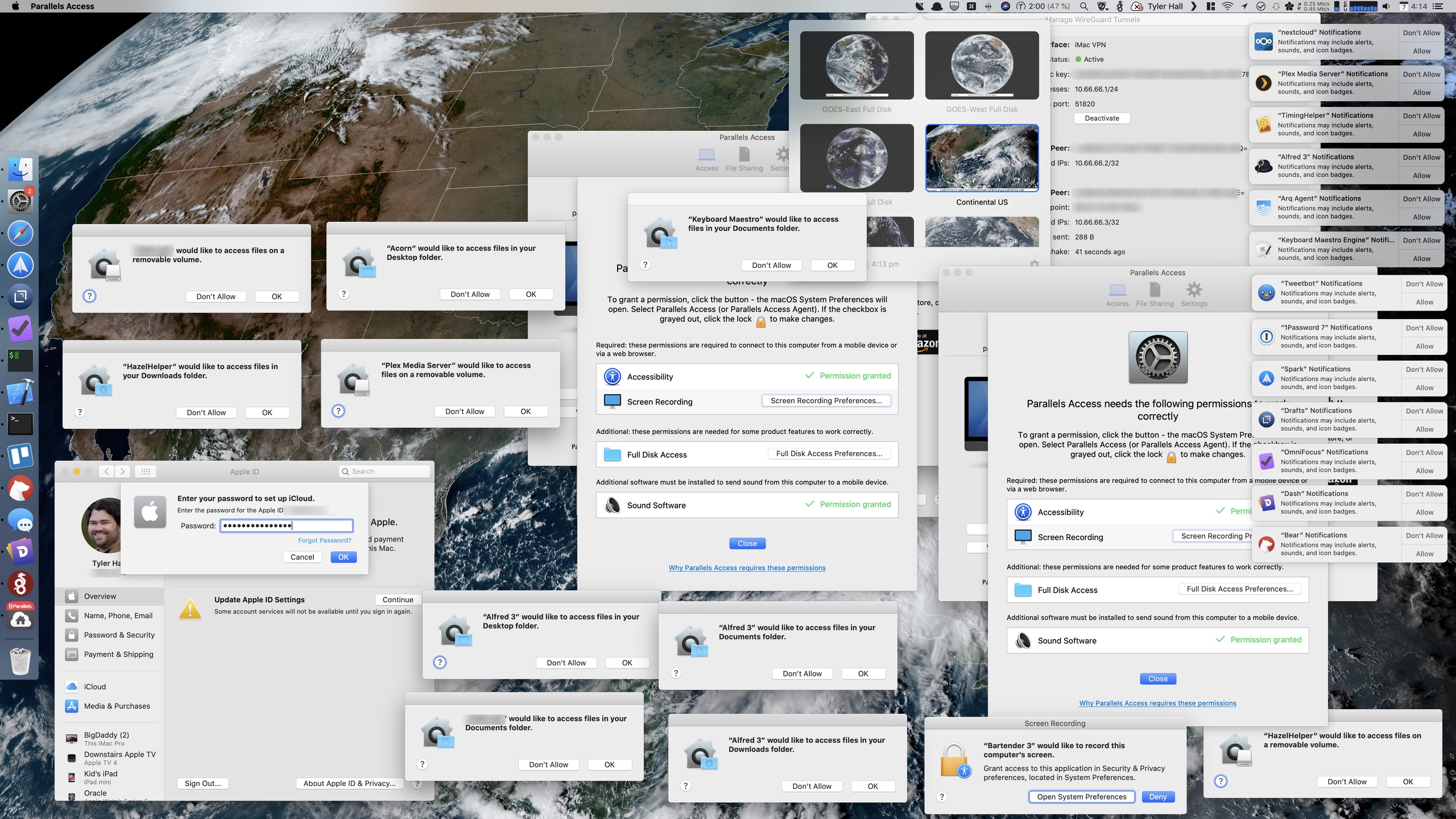
In macOS 10.15 Vista (1 min) and Broken (2 min, via), Tyler Hall presents a screenshot of evidence of how low Apple has fallen with its recent UX.
I will definitely not upgrade to Catalina, and there are many others who think like me
I sincerely hope Apple get its act together and starts producing good software and hardware again. These last 5 years have been an absolute hell as an Apple ecosystem user.
Cloudflare is bad, take two 🔗
CloudFlare is ruining the internet (for me) (2016, 2 min, via)
The idea that a single company can negatively influence the experience of such a large portion of the internet for users is kinda scary
I agree with the author. We should stop giving Cloudflare too much power.
This is a company that can cut off internet access for a large amount of users, or seriously hinder it (endless stream of captchas) with the switch of a button.
I would urge everyone to reconsider using CloudFlare as your CDN/DNS/DDOS solution. Being free is not good enough reason to use something, if you are concerned about your site speed there are more important things to look into for optimization before considering a CDN
Most deepfakes are porn 🔗
Most Deepfakes Are Used for Creating Non-Consensual Porn, Not Fake News (2 min, via)
We need to figure out how platforms will moderate users spreading malicious uses of AI, and revenge porn in general. We have to solve the problems around consent, and the connection between our bodily selves and our online selves. We need to face the fact that debunking a video as fake, even if it's proven by DARPA, won't change someone's mind if they're seeing what they already believe. If you want to see a video of Obama saying racist things into a camera, that's what you'll see—regardless of whether he blinks.
The Department of Defense can't save us. Technology won't save us. Being more critically-thinking humans might save us, but that's a system that's lot harder to debug than an AI algorithm.
Last month I linked to a Facebook initiative to detect deepfakes and it seems that the deepfake problem is starting to get mainstream.
Good.
Tags: roundup